Secure execution framework
An idea I’ve been toying with the last couple of months, sparked by conversations with Bijay: Is there true privacy in the world ? What does that even mean ?
I think this is the key question of our decade.
We only see copies of data today, not really the authentic source of truth. In fact even seeing something with our eyes is making a copy of it in our memory. The next time you’re describing it to someone else, you’ll be referring to bits and pieces of your memories about the object you saw. If it’s a car, you’ll describe the color, the shape, the texture, the overall driving experience.
If you clicked a picture of the car, you could share the picture with your friends to show them what the car looks like, from multiple angles. More copies of data are created. Your friend could create a local copy and share that with his friends, and now suddenly you have lost control over the information being shared.
True ownership of something should imply being the sole authority in control of it. You and only you should be able to prove ownership of the asset.
Like with Zero Knowledge proofs, it’s trivial to prove you own something by showing it, the challenge is to prove ownership without disclosing the asset (and the mechanics behind it).
Nothing is truly private
Ever notice that people treat you differently if you disclose your political affiliations, or your religious beliefs ? For example if go to a job interview dressed in a heavy religious attire, chances are you’ll get a lot of undue attention. What if you go to a job interview wearing a cap of your favorite political party ?
One logical way of thinking about it is that the recipient having known little about you before, is seeing you dressed in a way that indicates that your political / religious affiliation matters to you more than the job, or the mechanics of your job. The reason why uniforms were introduced were to unite a diverse group of people to a common cause - the job. And by not dressing for it, you are indicating what matters more to you.
So even though you might be a staunch supporter of party X, it may not be in your best interest to disclose it, especially wear your affiliation. You may want this to be private to you. Only for you to share it with people you feel comfortable with.
Only for you to share it with people you feel comfortable with
But what if a friend you share your political beliefs with were to share it with your potential employer at the time of a background check ? Not only does this happen all the time, the background check process is super important to ensure the authenticity of the individual applying for the job, and to verify that he is who he claims to be, and has the skills he claims to have. That’s kind of the point of a background check !
And so we come to a hard realization that nothing thats shared is truly private in this world. Only your inner thoughts that you have never written down could be classified as truly private, almost everything else can (or already has) been copied, backed up somewhere. Even encryption doesn’t guarantee complete privacy because if implemented weekly, it can be broken by brute force in say a 100 year time frame. I’d die before my encrypted information is hacked and misused, but my future generations may be alive and might pay the price for it. True privacy would be ensuring that nobody apart from me has the information (or an encrypted copy of it) at all.
Information is useless if it can’t be shared / mutated
There was a saying that PDF is where data goes to die. 10 years back, pdf’s were almost impossible to modify. They were a great way of sharing data, but pretty soon people realized that anything mainstream of importance would be constantly mutating. If you don’t update something, it’ll soon be obsolete. If you stop referring to the obsolete copy of the data, it’s dead.
The point is, valuable data and information is shared a lot. The key question is, how can I share information while still being in control of it ?
Here are some real world examples to think about:
Would you publicly announce your blood type, and the fact that you’ve registered to be an organ donor ?
Do you want a Gmail hack to expose sensitive information like your house passcode, your bank account details etc.
Should critical health related data like missed periods, testing positive for HIV be available to governments ?
Should political affiliations be available to governments for them be able to spy on ?
If you answer NO to any of the above questions, I suggest going back to your email provider and asking them what’s the chances of your data being leaked ?
Time Berners Lee & Solid
Just read about Inrupt and Solid. Seems like a great spec to own data (in a pod), choose the pod provider, a way to authenticate and authorize data sharing.
Am still wondering about data ownership though. If data is shared with someone else, what stops them from creating a copy of it and sharing it with other untoward parties.
Interesting thing that AMD has come up with - AMD Secure Encrypted Virtualization, a way of encrypting information in memory (RAM). Google is extending this offering as Confidential computing. They have a case study with AstraZenca.
Here’s an excerpt from https://confidentialcomputing.io/:
Today, data is often encrypted at rest in storage and in transit across the network, but not while in use in memory. Additionally, the ability to protect data and code while it is in use is limited in conventional computing infrastructure. Organizations that handle sensitive data such as Personally Identifiable Information (PII), financial data, or health information need to mitigate threats that target the confidentiality and integrity of either the application or the data in system memory.
Secure execution frameworks
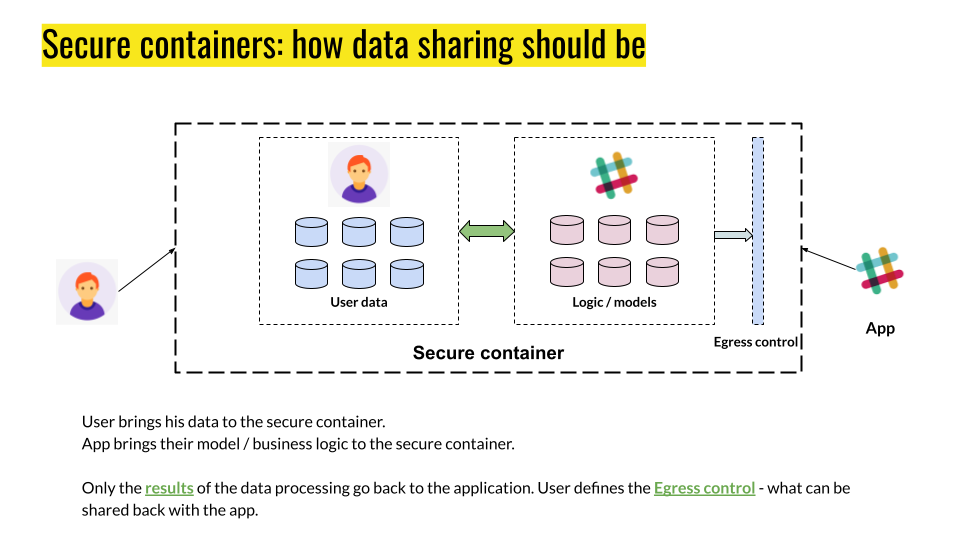
What if instead of sharing the data, you could bring the app / model to the data inside the pod itself. If data is not being shared, but only the result of the computation is, doesn’t that offer better data control & ownership ?
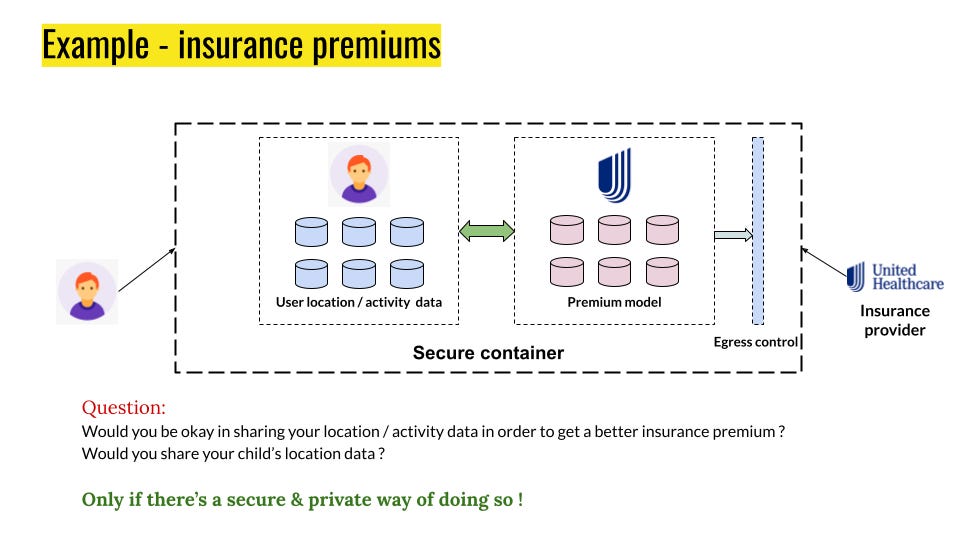
Here’s an example: sharing health records for better insurance premiums.
<more to come here …>